Intellectual Property (IP) Protection
Securing your CAD data
Today many companies believe, that Digital Rights Management (DRM) is enough to protect your IP. But this is not valid for CAD geometries. After having entered a password they will be unencrypted on your hard disk and when displaying them on screen using DirectX, OpenGL or WebGL, then they might get captured easily. So we need a different way to protect your IP.
Change geometries:
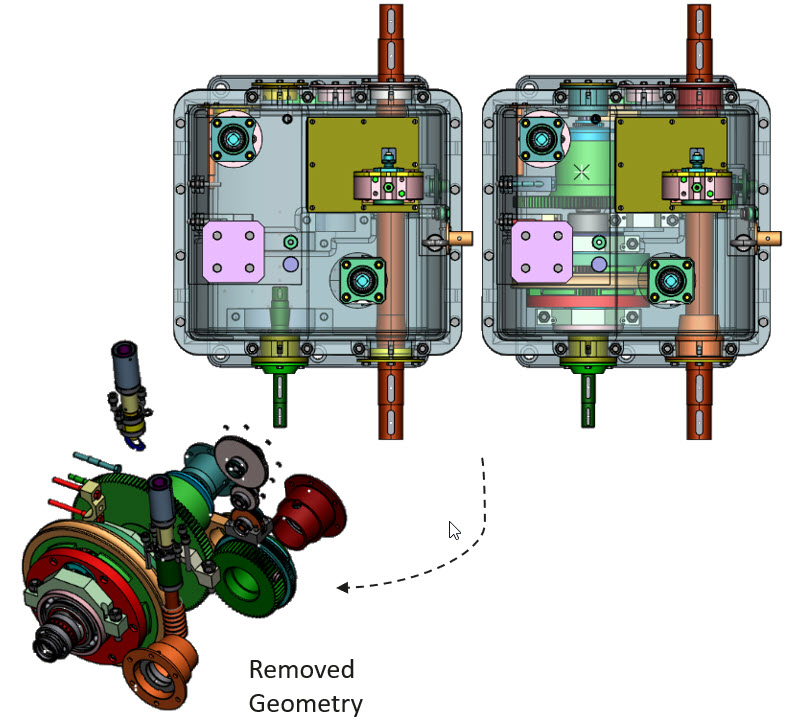
- remove invisible objects
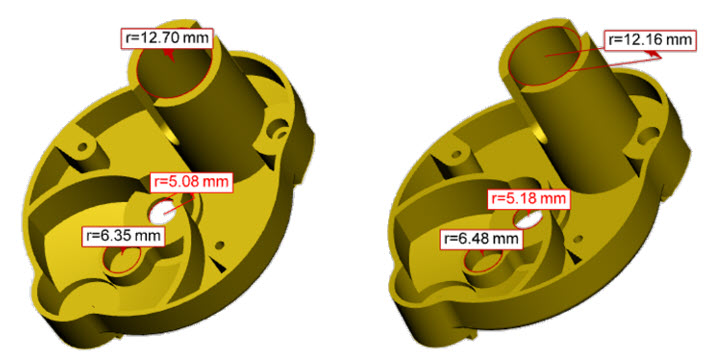
- automatic distortion of BREP and tesselated data. Set parameters to determine the degree of alientation. Objects might still look nice, but all dimenstions have been alienated.
- convex hull calculation
- very fast
- available as interactive or batch function
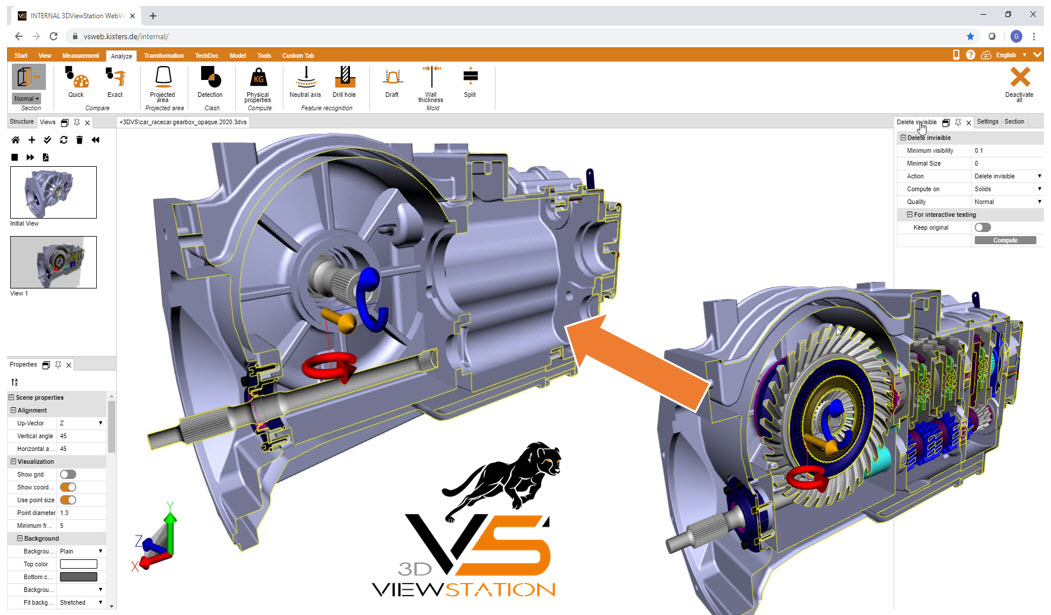
Visualization leveraging 3DViewStation WebViewer:
- secure Web-based viewing
- avoid forwarding of geometry files to communication partners, give remote access instead
- at no time there will be any 3D objects on the client, impossible to capture
- we only use server side rendering
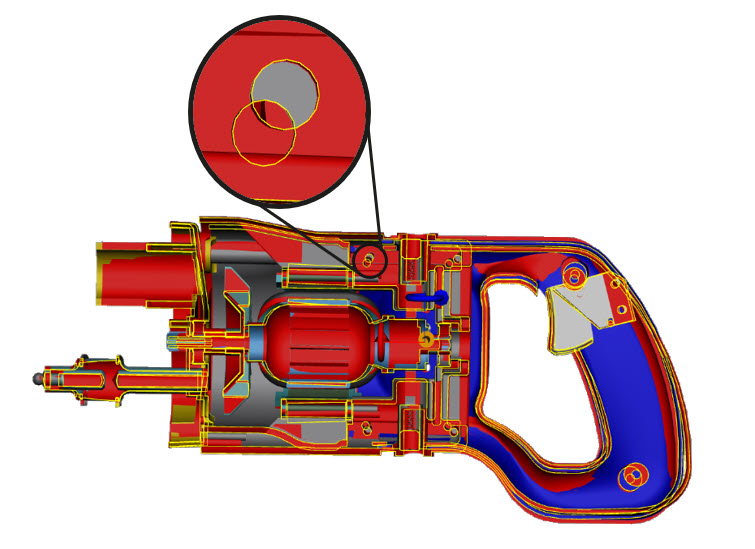
- prevent certain parts from sectioning
How can I protect my intellectual property technically and effectively when I really need to share CAD files?
Various techniques must be used to protect the intellectual property of 3D CAD data. Some effective ones are:
- Automatic removal of non-visible geometry in CAD data refers to the use of techniques to remove parts or elements of a CAD model that are not visible and almost not visible from the outside. As a side effect, this can reduce the size and complexity of the model.
- Geometric simplification involves reducing the level of detail in 3D CAD data. This can be achieved not only by removing parts that are not visible, but also by simplifying complex geometries or reducing the number of polygons in the model. This makes it more difficult for unauthorized users to reverse engineer the model.
- Another process is the removal of features or details from the model. This can be done by deleting certain elements or smoothing surfaces. This makes the model simpler and less recognizable.
- Automatic alienation of 3D CAD geometries: This is sometimes referred to as "geomorphing" and is a technique of automatically changing the shape or appearance of 3D models to protect them from unauthorized copying or reverse engineering.
- Obfuscation is a technique in which noise or complexity is intentionally added to 3D CAD data. This makes it more difficult for unauthorized users to understand or extract valuable information from the data.
- Distorting the original geometry to create new shapes and patterns. This can be done by applying deformation tools or by manually editing the geometry.
- Scaling, emans enlarging or reducing the geometry to achieve a specific effect. This can help draw attention to specific details or make the geometry more eye-catching overall.
- Intentionally introducing asymmetry into geometry to create an unexpected or unique design element. This can be achieved by removing axes of symmetry or adding non-uniform patterns and textures.
- Applying textures to the surface of geometry to create a specific visual or tactile feel. This can be done by adding patterns, cracks or scratches.
- Do not pass on the data in the native, i.e. original data format, but convert it to another format. A common neutral format is STEP, which also allows to store BREP, i.e. the exact geometry. Or use data formats for tessellated representations, such as JT or STEP-tessellated.
It is important to note that these steps can help minimize the risks associated with sharing CAD files, but they cannot guarantee complete protection of your intellectual property. Therefore, it is important to exercise caution and good judgment when sharing sensitive information and consider whether the sharing itself is truly necessary and can be avoided if necessary.
What can I do to prevent access to sensitive information when I only need to view / visualize 3D CAD files?
In many processes of the manufacturing industry, the disclosure of CAD data is not necessary. It is sufficient to only allow the view of the data, to view it. For visualization purposes, the best solution is a combination of measures:
- If you need to share 3D CAD files containing sensitive information, then you should use a secure file-sharing platform that provides encryption, access control and other security features. An example is Kisters' VisShare solution or web client of various PLM systems.
- Where possible, use only tessellated data. It is very time-consuming to generate BREP and thus production-ready data from this triangulated data via reverse engineering.
- Use secure display tools with server-side rendering, means tools designed to protect sensitive information. Like Kisters 3DViewStation WebViewer. These tools ideally prevent downloading 3D geometry for local rendering. Instead, the 3D CAD data is rendered exclusively on the server and only an image or video stream is sent to the client device.
- Data can be alienated so cleverly that it is hardly or not at all noticeable when displayed in the viewer. Often it is sufficient to alienate only the particularly sensitive areas and to leave the rest. Good CAD viewers such as 3DViewStation allow to alienate the data even at runtime via API functions, i.e. remotely. Of course, this can also be done in advance in a batch.
- Secure viewers such as Kisters 3DViewStation allow you to prevent certain components from being cut. Thus, the internal know-how is protected. Which parts or assemblies may be cut can be stored in the form of metadata, e.g. in the leading system.
- 3DViewStation and also the batch tool KAS allow to remove objects that are not or hardly visible from the outside. This can be parameterized. This way you don't need to prevent certain geometries from being cut anymore.
- Another method is the use of "Level of Detail" (LOD) techniques. This involves dividing the model into different levels of detail, with each level having a different level of detail. For very sensitive data, a coarser level of detail can be specifically selected in the viewer.
With Kisters 3DViewStation and if necessary in combination with our batch tool KAS you are always on the safe side when it comes to handling sensitive CAD data. No matter whether on desktops or in the browser. Whether internally or in communication with external partners.
Common measures for know-how protection / IP protection
In addition to those mentioned above, there are various general methods of intellectual property (IP) protection that can also be used to protect 3D CAD data, including:
- Patents protect new and non-obvious inventions, including new designs and processes. So if your 3D CAD data is related to a new and non-obvious invention, consider filing a patent application. Registering your intellectual property with the appropriate authorities can provide you with legal protection and prevent infringement.
- Trade secrets protect confidential information that gives a company a competitive advantage. If your 3D CAD data includes proprietary design or manufacturing processes, you should protect this information as a trade secret.
- Non-disclosure agreements (NDAs) are legal agreements between parties to keep confidential information secret. You should consider requiring NDAs for anyone who has access to your 3D CAD data, such as employees or contractors.
- Watermarking involves adding a visible or invisible mark to your 3D CAD data to identify the owner. This requires the design team to use CAD tools such as Catia or SolidWorks to modify the CAD data internally without being easily visible to the outside world.
- Use encryption to protect your CAD files during transfer and storage. This helps prevent unauthorized access and distribution.
- Digital rights management (DRM) is a set of technologies and strategies for protecting digital content from unauthorized access or use. You should consider using DRM software to control who has access to your 3D CAD data and what they can do with it.
- It's always reasonable to restrict access: Share CAD files only with people or organizations that absolutely need to access them. This reduces the risk of unauthorized access and distribution of your intellectual property.
- And regularly monitor accesses and usage of your CAD files to ensure that they are only being used for their intended purpose and that there are no violations of your IP rights.
All of these methods are certainly useful, but they are not technically suitable for preventing the recipient of this data from using it to illegally manufacture and market products, for example, and thereby harming the owner.